Видео с ютуба Black Hat 2013

Black Hat 2013 - Exploiting Network Surveillance Cameras Like a Hollywood Hacker

Black Hat USA 2013 Keynote - Gen. Alexander

Black Hat 2013 - Welcome & Introduction to Black Hat USA 2013

Black Hat USA 2013 - SSL, gone in 30 seconds - a BREACH beyond CRIME
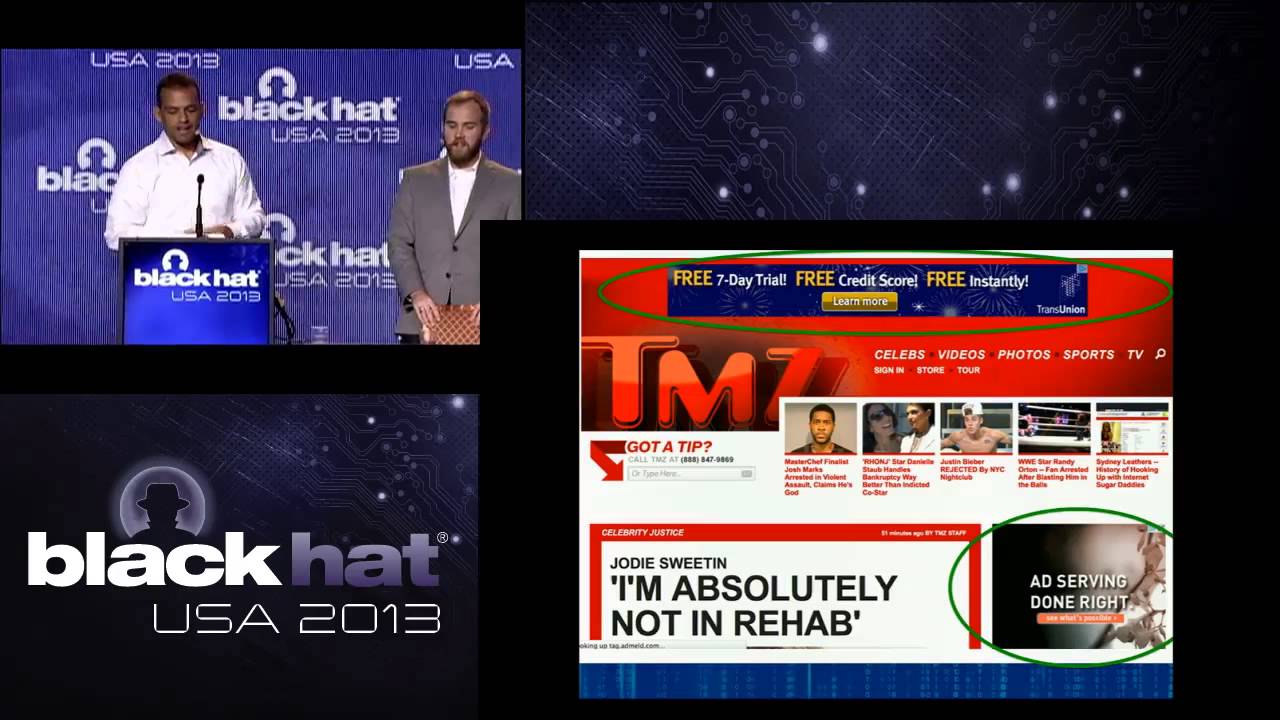
Black Hat 2013 - Million Browser Botnet

Black Hat 2013 - How to Build a SpyPhone

Black Hat 2013 - TOR... ALL-THE-THINGS!

Black Hat 2013 - The Outer Limits: Hacking The Samsung Smart TV

Black Hat USA 2013 - Hacking like in the Movies: Visualizing Page Tables for Local Exploitation

Black Hat 2013 - BIOS Security

Black Hat 2013 - OPSEC Failures of Spies

Black Hat 2013 - Mainframes: The Past Will Come to Haunt You

Black Hat 2013 - Stepping p3wns: Adventures in Full Spectrum Embedded Exploitation

Black Hat 2013 - PWNIE AWARDS

Black Hat USA 2013 - Pixel Perfect Timing Attacks with HTML5

Black Hat USA 2013 - Out of Control: Demonstrating SCADA device exploitation

Black Hat USA 2013 - Android: one root to own them all

Black Hat USA 2013 - Hunting the Shadows: In Depth Analysis of Escalated APT Attacks

Black Hat USA 2013 - CreepyDOL: Cheap, Distributed Stalking

Black Hat USA 2013 - Lessons from Surviving a 300Gbps Denial of Service Attack

Black Hat 2013 - Spy-jacking the Booters

Black Hat USA 2013 - CrowdSource: Crowd Trained Machine Learning Model for Malware Capability Det.

Black Hat 2013 - Rooting SIM Cards

Black Hat USA 2013 - Let's get physical: Breaking home security systems & bypassing controls

Black Hat 2013: Why Are Network Administrators Behind the Cyber Criminals?